Jensen-based New Cryptographic Scheme
Keywords:
Jensen Polynomials, Laplace Transform, Cryptographic algorithm, Information security, Cryptographic SchemeAbstract
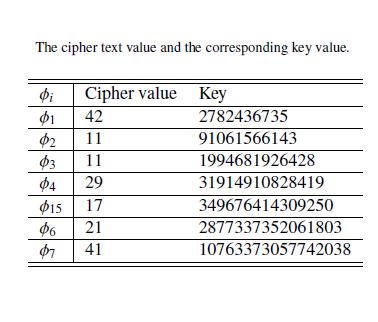
The surgent availability of data and the demand for more data to implement several technological products which heavily depends on data have made the issue of cyber attacks, a global threat, of great concern. To ensure the protection of information, the heart of every nation, the development of formidable techniques which contribute to the advancement of present schemes is crucial to combat the challenge. In this research work, a mathematical framework, from the idea of cryptography, is developed using Jensen polynomial. Jensen polynomial is used for the encryption algorithm, and the Laplace transform is used as a transformation tool to convert the plain text message to cipher text message. The decryption is a reversal which involves the use of structured mathematical techniques and the key for the message.
Published
How to Cite
Issue
Section
Copyright (c) 2022 Journal of the Nigerian Society of Physical Sciences

This work is licensed under a Creative Commons Attribution 4.0 International License.
How to Cite
Similar Articles
- Olayiwola Babarinsa, Olalekan Ihinkalu, Veronica Cyril-Okeme, Hailiza Kamarulhaili, Arif Mandangan, Azfi Zaidi Mohammad Sofi, Akeem B. Disu, Application of hourglass matrix in Goldreich-Goldwasser-Halevi encryption scheme , Journal of the Nigerian Society of Physical Sciences: Volume 4, Issue 4, November 2022
- Philemon Uten Emmoh, Christopher Ifeanyi Eke, Timothy Moses, A feature selection and scoring scheme for dimensionality reduction in a machine learning task , Journal of the Nigerian Society of Physical Sciences: Volume 7, Issue 1, February 2025
- A. E. Ibor, E. B. Edim, A. A. Ojugo, Secure Health Information System with Blockchain Technology , Journal of the Nigerian Society of Physical Sciences: Volume 5, Issue 2, May 2023
- K. Issa, A. T. AbdulKareem, A D. Adeshola, R. A. Bello, Numerical solution of fractional advection-diffusion equation with generalized Caputo derivative using shifted ultraspherical collocation method , Journal of the Nigerian Society of Physical Sciences: Volume 8, Issue 2, May 2026 (In Progress)
- Emmanuel Adeyefa, O. S. Esan, Exponentially Fitted Chebyshev Based Algorithm as Second Order Initial Value Solver , Journal of the Nigerian Society of Physical Sciences: Volume 2, Issue 1, February 2020
- Olalekan Taofeek Wahab, Salaudeen Alaro Musa, AbdulAzeez Kayode Jimoh, Kazeem Adesina Dauda, Constructive approach and randomization of a two-parameter chaos system for securing data , Journal of the Nigerian Society of Physical Sciences: Volume 6, Issue 2, May 2024
- S. N. Enemuo, O. N. Akande, M. O. Lawrence, I. C. Saidu, Optimized aspect level sentiment analysis of tweet data using deep learning and rule-based techniques , Journal of the Nigerian Society of Physical Sciences: Volume 7, Issue 2, May 2025
- Umaru C. Obini, Chukwu Jeremiah, Sylvester A. Igwe, Development of a machine learning based fileless malware filter system for cyber-security , Journal of the Nigerian Society of Physical Sciences: Volume 6, Issue 4, November 2024
- Unyime Ufok Ibekwe, Uche M. Mbanaso, Nwojo Agwu Nnanna, Umar Adam Ibrahim, A machine learning sentiment classification of factors that shape trust in smart contracts , Journal of the Nigerian Society of Physical Sciences: Volume 7, Issue 1, February 2025
- K. Issa, A. S. Olorunnisola, O. T. Aliu, A. D. Adeshola , Approximate solution of space fractional order diffusion equations by Gegenbauer collocation and compact finite difference scheme: Solution of space fractional diffusion equation , Journal of the Nigerian Society of Physical Sciences: Volume 5, Issue 2, May 2023
You may also start an advanced similarity search for this article.