Jensen-based New Cryptographic Scheme
Keywords:
Jensen Polynomials, Laplace Transform, Cryptographic algorithm, Information security, Cryptographic SchemeAbstract
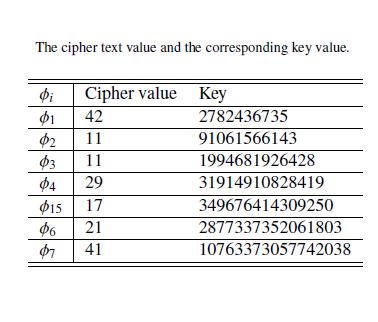
The surgent availability of data and the demand for more data to implement several technological products which heavily depends on data have made the issue of cyber attacks, a global threat, of great concern. To ensure the protection of information, the heart of every nation, the development of formidable techniques which contribute to the advancement of present schemes is crucial to combat the challenge. In this research work, a mathematical framework, from the idea of cryptography, is developed using Jensen polynomial. Jensen polynomial is used for the encryption algorithm, and the Laplace transform is used as a transformation tool to convert the plain text message to cipher text message. The decryption is a reversal which involves the use of structured mathematical techniques and the key for the message.
Published
How to Cite
Issue
Section
Copyright (c) 2022 Journal of the Nigerian Society of Physical Sciences

This work is licensed under a Creative Commons Attribution 4.0 International License.
How to Cite
Similar Articles
- Olugbenga Oludayo Oluwasina, Analysis of Adenanthera pavonine L. (Febaceae) Pod and Seed as Potential Pyrolysis Feedstock for Energy production , Journal of the Nigerian Society of Physical Sciences: Volume 4, Issue 2, May 2022
- Rauf I. Rauf, Ayinde Kayode, Bello A. Hamidu, Bodunwa O. Kikelomo, Alabi O. Olusegun, Enhanced methods for multicollinearity mitigation in stochastic frontier analysis estimation , Journal of the Nigerian Society of Physical Sciences: Volume 6, Issue 4, November 2024
- Gabriel O. Odekina, Adedayo F. Adedotun, Ogbu F. Imaga, Modeling and Forecasting the Third wave of Covid-19 Incidence Rate in Nigeria Using Vector Autoregressive Model Approach , Journal of the Nigerian Society of Physical Sciences: Volume 4, Issue 1, February 2022
- Lamees K. Alzaki, Hassan Kamil Jassim, Time-Fractional Differential Equations with an Approximate Solution , Journal of the Nigerian Society of Physical Sciences: Volume 4, Issue 3, August 2022
- Idongesit E. Eteng, Udeze L. Chinedu, Ayei E. Ibor, A stacked ensemble approach with resampling techniques for highly effective fraud detection in imbalanced datasets , Journal of the Nigerian Society of Physical Sciences: Volume 7, Issue 1, February 2025
- A. B. Disu, S. O. Salawu, Thermal distribution of magneto-tangent hyperbolic flowing fluid over a porous moving sheet: A Lie group analysis , Journal of the Nigerian Society of Physical Sciences: Volume 5, Issue 1, February 2023
- Xiaojie Zhou, Majid Khan Majahar Ali, Farah Aini Abdullah, Lili Wu, Ying Tian, Tao Li, Kaihui Li, Air quality prediction enhanced by a CNN-LSTM-Attention model optimized with an advanced dung beetle algorithm , Journal of the Nigerian Society of Physical Sciences: Volume 7, Issue 3, August 2025
- Ebere Uzoka Chidi, Edward Anoliefo, Collins Udanor, Asogwa Tochukwu Chijindu, Lois Onyejere Nwobodo, A blind navigation guide model for obstacle avoidance using distance vision estimation based YOLO-V8n , Journal of the Nigerian Society of Physical Sciences: Volume 7, Issue 1, February 2025
- Kazeem adebowale Dawodu, Extension of ADMMAlgorithmin Solving Optimal Control Model Governed by Partial Differential Equation , Journal of the Nigerian Society of Physical Sciences: Volume 3, Issue 2, May 2021
- Kashif Hussain, Oluwaseun Adeyeye, Nazihah Ahmad, Numerical Solution of Second Order Fuzzy Ordinary Differential Equations using Two-Step Block Method with Third and Fourth Derivatives , Journal of the Nigerian Society of Physical Sciences: Volume 5, Issue 2, May 2023
You may also start an advanced similarity search for this article.